An operational plan is a plan that is intentionally created to guide every day tasks and activities that specific groups or teams have to do to help the company or organization reach its goals and objectives. The goals and objectives of an operational plan must support the goals and objectives of the organization’s strategic plan and tactical plan. So planning for the day-to-day operations of a group or team is aimed at helping the company or organization slowly get things done according to plan.
Sample Security Operational Plan Template
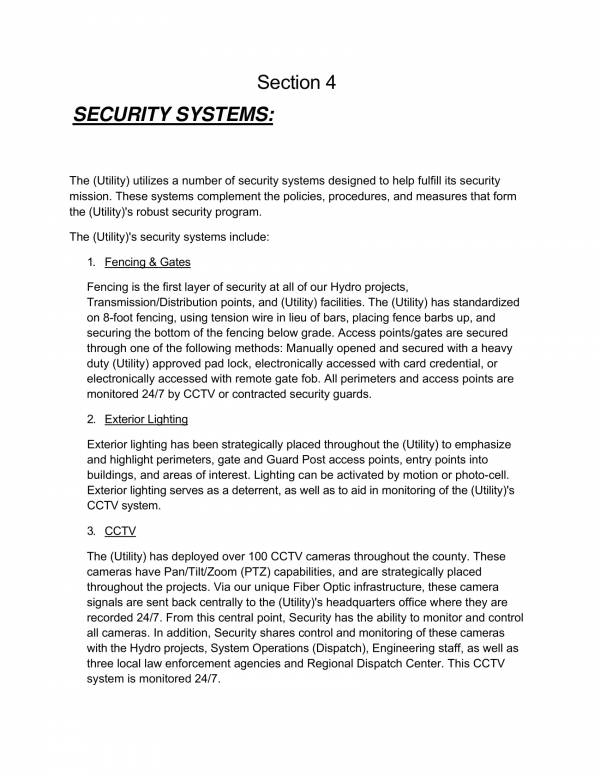
Safety and Security Operational Plan
Security Operational Plan Sample
There are many types of operational plans as it is used in specific areas and different groups within a company or organization. All of these operational plans are equally important and useful as long as they are planned used correctly in their respective areas.
One of these operational plans which we will be focusing on is a security operational plan. Here, we will find out what it is, its uses, the fives steps of operational security and its best practices. Security operational plan templates and samples have also been included to serve as your reference while going through this article. You may check them out below.
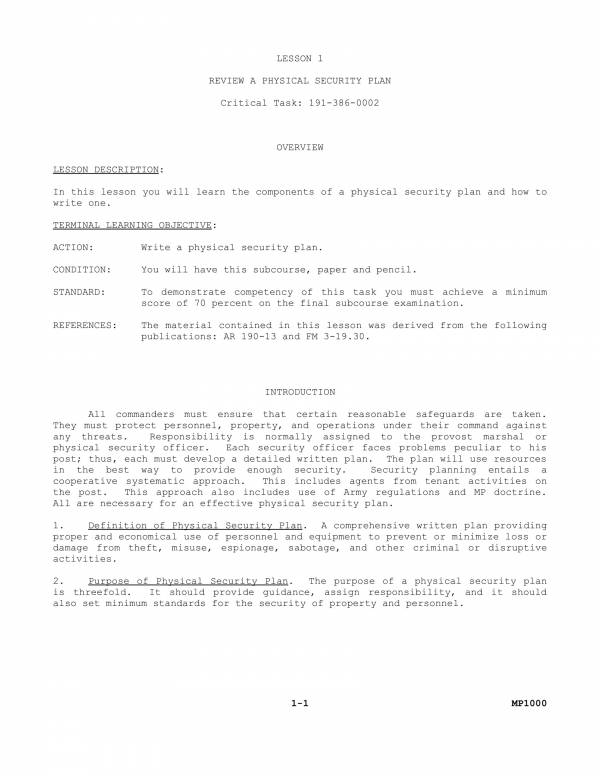
Physical Security Plan Template
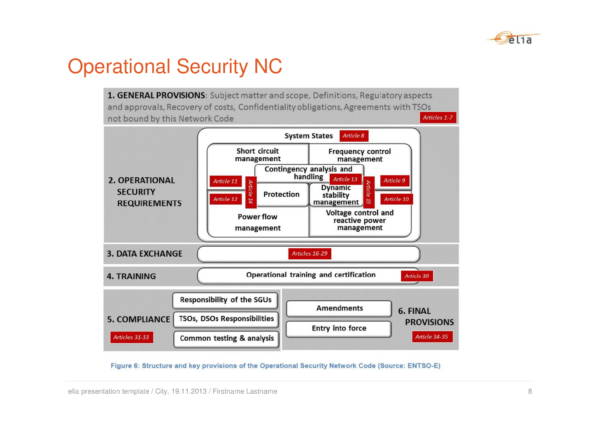
Editable Operations Security Plan
Campus Operational Security Plan
Security Operational Plan Example
What Is Operational Security?
Operation security was original used by the military during the Vietnam as an operation to investigate why certain combat operations fail during that time. The United State Military also coined the term operational security for that reason. The operations involved personnel coming from different security agencies in the United States, namely the Department of Defense and the National Security Agency.
The process was is still being used by the military to this date and various companies or organizations. Operational security or OPSEC is now a process that is used to determine or identify any risks that a company or organization is facing. It aims to protect confidential and proprietary information from people who are not involved or who have nothing to do with the company or organization. This also prevents important company information from falling into the wrong hands. The activities that fall under operational security are reminding employees to not share their log in credentials to other employees and monitoring their online and social media activities that may possibly affect work.
Other related articles you might want to check out are Simple Operational Planning Samples & Templates and Sales Plan Samples & Templates.
Uses of an Operational Plan
Operational plans vary from one industry or institution to another. They provide very detailed plan or set of information about the work or tasks to be done to reach specific goals and objective. Because of this, it has been proven to be a useful tool and has helped a lot of companies or organizations to reach its desired goals. To learn more about operational plan, let us check out its many different uses below.
- Risk management and reduction is one of the reasons why a security operational plan is used by many companies and organizations, regardless if they have a big or small population. It is the responsibility of the management of a company or organization to ensure the safety of all their employees, as well as their assets and trade secrets. With the use of a security operational plan, all confidential and propriety information are secured and protected by all possible means.
- Big or small projects need a thorough and detailed plan before it is carried out to ensure that everything is being worked on in a timely fashion. Project operational plans are used to direct all of the people involved in a certain project on who should do what tasks and how should the tasks be done. This provides and organized and uniform way of doing things which is very important to finish the project on time and make sure that the desired outcomes are met.
- The human resources department also have their own HR operational plan to follow. This allows them to do all of the many demanding tasks required of them within a company or organization, especially those who have a large population. The operational helps them delegate recruitment tasks and human resources tasks to meet their goals and objectives on time.
- A long term operational plan such as an annual operational plan is used to set a long term goal that particular teams or groups follow to accomplish tasks.
- Schools also make use of operational plans to guide them with their day-to-day school activities. Schools are made of different groups of people who have their won specific functions. Providing a single plan for everybody may cause the entire school to become chaotic and disorganized. School operational plans allow different departments and department heads to plan out the specific things that they need to do according to the goals and objectives of the school as a whole.
The uses of an operational plan depends on the industry and organization it is being used on. Regardless of what it is, it sure is a very useful planning tool.
Five Steps of Operational Security
There are five steps involved in planning for operational security. It is important to know of these five steps in order to be able to properly plan for it and implement it based on appropriate standards. The five steps are identification of sensitive data or critical information, identification and analysis of possible threats, analysis of vulnerabilities, risk assessment, and application of appropriate operational security measures.
- Identification of sensitive data or critical information – This step is taken so that the focus of the security plan is aimed at protecting critical and vital classified information, instead of attempting to protect all other information. Putting focus on information that matters allows the company or organization to provide a reliable protection. These critical information, includes customer and employee information, trade secrets, intellectual property, product research, financial statements, etc.
- Identification and analysis of possible threats – Threats are those things, people and activities that pose potential harm to the safety of a company or organization. Identifying these threats and being able to analyze them will helping creating safety plan and implementation strategies. We also see threats as outsiders or third party entities who are trying to steal information, but there are also threats coming form the inside that you should be aware of. Examples of these threats are employees who neglect their jobs and violate rules, dissatisfied or demotivated employees and many more.
- Analysis of vulnerabilities – Knowing any loopholes that your company or organization has or its security measures has allows you to prevent unauthorized access to any important. Loopholes or weaknesses can be exploited by competitors or outsider and use it to gain inside information.
- Risk assessment – Determining and prioritizing risks can help you prepare for what will will happen ahead of you. You will be able to plan on possible attacks and mitigate the risks that can make the attack possible.
- Application of appropriate operational security measures – This is the last step of the operational security process. In this step, implementation of the plan is carried out to eliminate or mitigate the possible threats, loopholes, weaknesses and vulnerabilities that has been identified. All employees should be aware of these counter measures and they should be able to have it implemented.
These five steps is everything that you need to have your security operational plan all set. Other related articles available on our website are Business Plans Samples & Templates and Marketing Plans in PDF.
Security Operational Plan
Sample Operational Security and Operational Planning
US Navy and Marine Operations Security
Joint Security Operational Plan
Overview of Operational Security Measures
What Are the Best Practices for Operational Security?
Regardless of what it is that you need to do, it is always good to follow the best practices when doing something. There are also best practices for the implementation of a good operational security. They are as follows.
- We often say that change is constant. When making certain changes to management, operation and company networks, it is important to ensure that all of the employees follow the new changes. Create a log for all of these changes which will serve as your record or as reference for monitoring.
- Employees should be provided access only to things that is related to their work and that allows them to do their job. If it is enough to perform their jobs then it will work.
- Don’t make all information available to all employees. Restrict their access to things that only involves them or on things where they are a part of.
- Humans are believed to be the weakest link when it comes to maintaining operational security. As much as possible, automate security processes that can be automated. This lessens the likelihood of security risks, threats, loopholes and vulnerability.
- It’s easy to pick people who work under you and assign them or make them in charge of security. But that is actually something you should not do. Assign another group of people or individual to take care of the security part of things.
- Always make sure to have a plan on how you can identify risks, how to manage them and how to mitigate or lessen potential damages.
Best practices will always be useful no matter what field or industry it is being used on, and whether it is for providing instructions or for planning and implementing certain things. We sure hope that you are able to learn something from this article. If so, you may also be interested in Test Plans Samples & Templates and Risk Management Plan Samples & Templates.
Related Posts
FREE 10+ Higher Education Lesson Plan Samples in MS Word | Pages | Google Docs | PDF
FREE 9+ 30-Day Marketing Plan Samples in PDF | MS Word | Apple Pages | Google Docs
FREE 3+ Sales Team Action Plan Samples in PDF | MS Word | Apple Pages | Google Docs
Marketing Plan For Small Business Samples
FREE 7+ Fashion Business Plan Samples in PDF
FREE 10+ Sprint Planning Samples In MS Word | Google Docs | PDF
FREE 10+ Wedding Planning Samples in MS Word | Apple Pages | Powerpoint | PDF
FREE 9+ Monthly Study Planner Samples in PSD | Illustrator | InDesign | PDF
FREE 9+ Sample Curriculum Planning Templates in PDF | MS Word
FREE 10+ Teacher Development Plan Samples in MS Word | Google Docs | Apple Pages | PDF
FREE 10+ Basketball Practice Plan Samples in PDF
FREE 12+ School Business Plan Samples in PDF | MS Word | Apple Pages | Google Docs
FREE 7+ Client Strategic Plan Samples in PDF | MS Word
FREE 11+ Trucking Business Plan Templates in PDF | MS Word | Google Docs | Pages
FREE 7+ Small Hotel Business Plan Samples PDF | MS Word | Apple Pages | Google Docs