10+ Information Security Report Samples
Information may need to be disseminated especially if it is for public use and consumption, but some information may need to be fully confidential especially if it involves personal records or company records or profiles. Almost all countries have already passed laws that are related to Data Privacy, other companies also ensure full confidentiality of their branding secrets that makes their product or services, distinct from others. With the upholding importance of information security, there is a need for close monitoring, constant or regular reports that would provide the management a comprehensive and detailed knowledge about the company’s data security. In making this possible, there needs to be an Information Security Report. To avoid doing this from the very scratch, our site offers you free, available and ready-made yet customizable templates that can suffice your needs for your report forms. Just browse among these templates and choose the one that satisfies your needs the most.
For other report template needs, our site offers templates like Monthly Status Report, Project Weekly Status Report, Weekly Construction Progress Report, Individual School Report, Problem Solving Report, Daily Sales Report, Action Research Report, Construction Feasibility Report, Network Feasibility Report, etc. Our article does not only give you free and ready-made templates but also provide you with ideas that are essential in making one. So what are you waiting for? Come! Read the article with me.
1. Information Security Report Sample
2. Printable Information Security Report
3. Standard Information Security Report
4. Group Information Security Report
5. Information Security and Cyber Security Report
6. Formal Information Security Report
7. Information Security Initiative Report
8. Professional Information Security Report
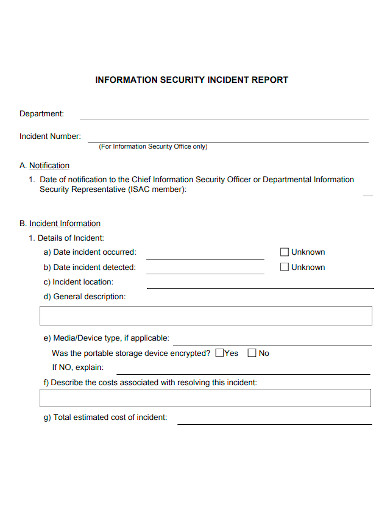
9. Information Security Incident Report
10. Information Security Report Format
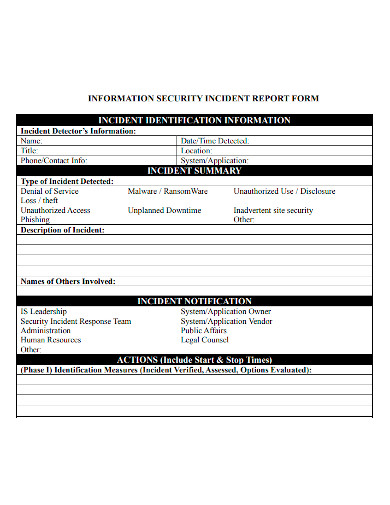
11. Information Security Incident Report Form
What Is Information Security?
Information Security refers to the processes and methodologies which are designed and implemented to protect print, electronic, or any other form of confidential, private and sensitive information or data from unauthorized access, use, misuse, disclosure, destruction, modification, or disruption. Information security, sometimes abbreviated to infosec, is a set of practices intended to keep data secure from unauthorized access or alterations, both when it’s being stored and when it’s being transmitted from one machine or physical location to another. You might sometimes see it referred to as data security. As knowledge has become one of the 21st century’s most important assets, efforts to keep information secure have correspondingly become increasingly important.
Principles Of Information Security
Confidentiality
This is perhaps the element of the triad that most immediately comes to mind when you think of information security. Data is confidential when only those people who are authorized to access it can do so; to ensure confidentiality, you need to be able to identify who is trying to access data and block attempts by those without authorization. Passwords, encryption, authentication, and defense against penetration attacks are all techniques designed to ensure confidentiality.
Integrity
This means maintaining data in its correct state and preventing it from being improperly modified, either by accident or maliciously. Many of the techniques that ensure confidentiality will also protect data integrity—after all, a hacker can’t change data they can’t access—but there are other tools that help provide a defense of integrity in depth: checksums can help you verify data integrity, for instance, and version control software and frequent backups can help you restore data to a correct state if need be. Integrity also covers the concept of non-repudiation: you must be able to prove that you’ve maintained the integrity of your data, especially in legal contexts.
Availability
This is the mirror image of confidentiality: while you need to make sure that your data can’t be accessed by unauthorized users, you also need to ensure that it can be accessed by those who have the proper permissions. Ensuring data availability means matching network and computing resources to the volume of data access you expect and implementing a good backup policy for disaster recovery purposes.
FAQs
What is the purpose of information security?
Information security is designed to protect the confidentiality, integrity and availability of computer system and physical data from unauthorized access whether with malicious intent or not. Confidentiality, integrity and availability are referred to as the CIA triad
What are examples of information security incidents?
Computer system intrusion. Unauthorized access to, or use of, systems, software, or data. Unauthorized changes to systems, software, or data. Loss or theft of equipment used to store or work with sensitive university data.
Making this report may be a hard task for anyone since it requires a lot of planning should cover most of the very important information that the management or supervisor should know. With this, to ease the burden of making everything from the very scratch, we highly encourage everyone to avail the templates or any resources that they could see online. So what are you waiting for? Avail our templates now!
Related Posts
FREE 12+ Sample Testing Reports in PDF MS Word
FREE 11+ Sample Security Resume Templates in PDF MS Word
FREE 9+ HIPAA Security Risk Analysis Templates in PDF MS Word
FREE 9+ Sample Incident Report Forms in MS Word PDF
FREE 8+ Accomplishment Report Samples in PDF
FREE 6+ Security Risk Assessment Samples in PDF
FREE 5+ Sample Situation Report Templates in PDF
FREE What Is an IT Incident Report? [ With Samples ]
FREE 14+ Sample Marketing Reports in MS Word Google Docs ...
FREE 12+ Sample Fire Incident Reports in PDF MS Word
FREE 9+ Security Proposal Samples in PDF
FREE 9+ Sample Security Resume Templates in MS Word PDF
FREE 8+ Security Policy Samples in MS Word PDF
FREE 7+ Sample Police Reports in MS Word PDF
FREE How to Create an Incident Report [12+ Samples]